Judging a Person by their Purse – The Hierarchy of Purse Brands: Tier 2. Part 1

Microsoft Office Vulnerabilities Used to Distribute FELIXROO - vulnerability database
UNIQORN/Results/TEXT/LC-QuAD2.0.json at main · ajesujoba/UNIQORN · GitHub

What is the hierarchy of luxury handbag brands? - Fashion Digest London
What is the hierarchy of luxury handbag brands? - Quora
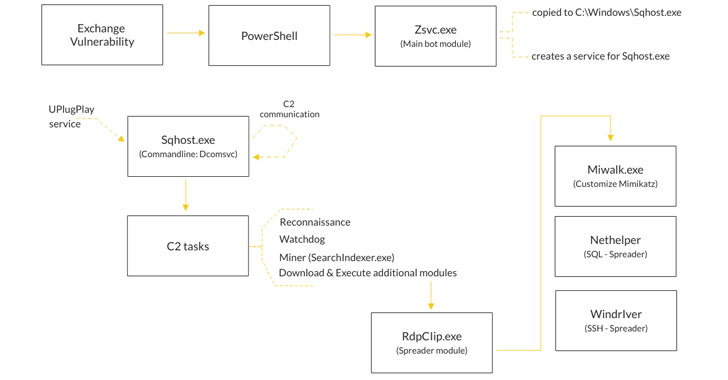
Prometei Botnet Exploiting Unpatched Microsoft Exchange Serv - vulnerability database
MuseumRecommendation/Data/review_quote_USonly.json at master · annecool37/MuseumRecommendation · GitHub

Judging a Person by their Purse – The Hierarchy of Purse Brands: Tier 2. Part 1
convai-bot-1337/notebooks/train_20170724.json at master · sld/convai-bot-1337 · GitHub

TAU Threat Advisory: Microsoft Exchange Servers Targeted wit - vulnerability database
cs224u-fp/data/kaggle/dev.csv at master · sebschu/cs224u-fp · GitHub
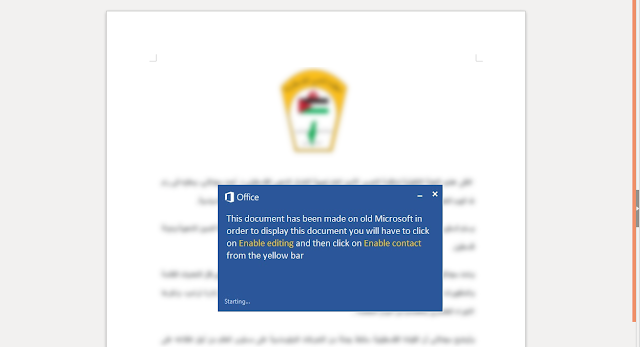
It's alive: Threat actors cobble together open-source pieces - vulnerability database
vnet/fixtures/2samples.json at master · Meelfy/vnet · GitHub
cookbook-2nd-data/troll.csv at master · ipython-books/cookbook-2nd-data · GitHub
Judging a Person by their Purse – The Hierarchy of Purse Brands: Tier 2. Part 1
- Best Price $ 5.00. Good quality and value when compared to palvarhaug.com similar items.
- Seller - 193+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Limited Edition Damier Couleur Modul Crossbody Bag - FIN – LuxeDH
Buy It Now 5d 6h -

Louis Vuitton Monterey II
Buy It Now 6d 18h -

Louis Vuitton Monogram Chain Bracelet
Buy It Now 3d 8h -

Louis Vuitton Néonoé
Buy It Now 28d 23h -

Guide for buying a pre-owned Louis Vuitton
Buy It Now 6d 9h -

Louis Vuitton Time Out Sneaker Cacao. Size 36.0
Buy It Now 28d 16h -

8 Designer Bags We Spotted In emily In Paris Season 2
Buy It Now 11d 10h -

Santa's Workshop Window – Fancy Fabric & Props
Buy It Now 9d 15h -

Louis Vuitton MY MONOGRAM ROUND SUNGLASSES Round sunglasses, Sunglasses, Louis vuitton
Buy It Now 17d 6h -

Takashi Murakami Louis Vuitton Scarf
Buy It Now 18d 10h -

Louis Vuitton - Boots - Size: Shoes / EU 38 - Catawiki
Buy It Now 11d 14h -

Large Intrecciato Tote Bag
Buy It Now 16d 9h -

Nike Air Force 1 '07 LV8 Sneaker in White - Size 9
Buy It Now 28d 9h -
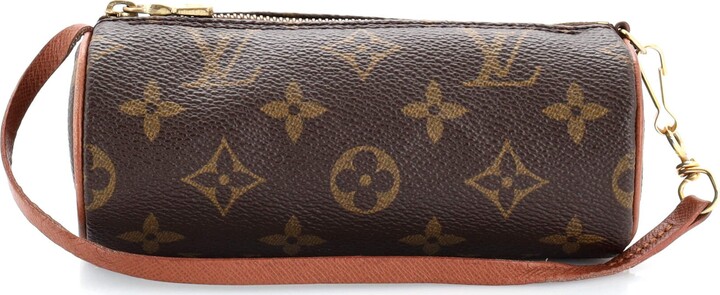
Louis Vuitton Papillon Pochette Monogram Canvas Mini - ShopStyle Clutches
Buy It Now 26d 11h -

6 Top Luxury Brand Logos With Meaning Explained - Clicked Studios
Buy It Now 5d 8h -

LV Trainer Sneaker - Men - Shoes
Buy It Now 12d 12h -
-5.jpg)
Every Sneaker Kanye West Ever Designed, Ranked
Buy It Now 27d 16h -

Louis Vuitton Utility Side Bag Monogram Brown
Buy It Now 2d 7h -

Louis Vuitton 2054 Expandable Polochon
Buy It Now 12d 21h -

EVURU Vintage Carving Leaf Earrings Metal Silver Color Blossom Inlaid Purple Stones Dangle Earrings for Women Gift 1Pair (Color : 002)
Buy It Now 28d 10h -

LOUIS VUITTON LV ZIPPER PULL CHARM GOLD tone metal , BLACK STONES
Buy It Now 3d 10h -
Virgil Abloh Teases New Off-White™ x Nike Hoodie Collab
Buy It Now 20d 16h -

Jean Lowe Matiere BY MAISON ALHAMBRA – Eau de parfum
Buy It Now 25d 22h -
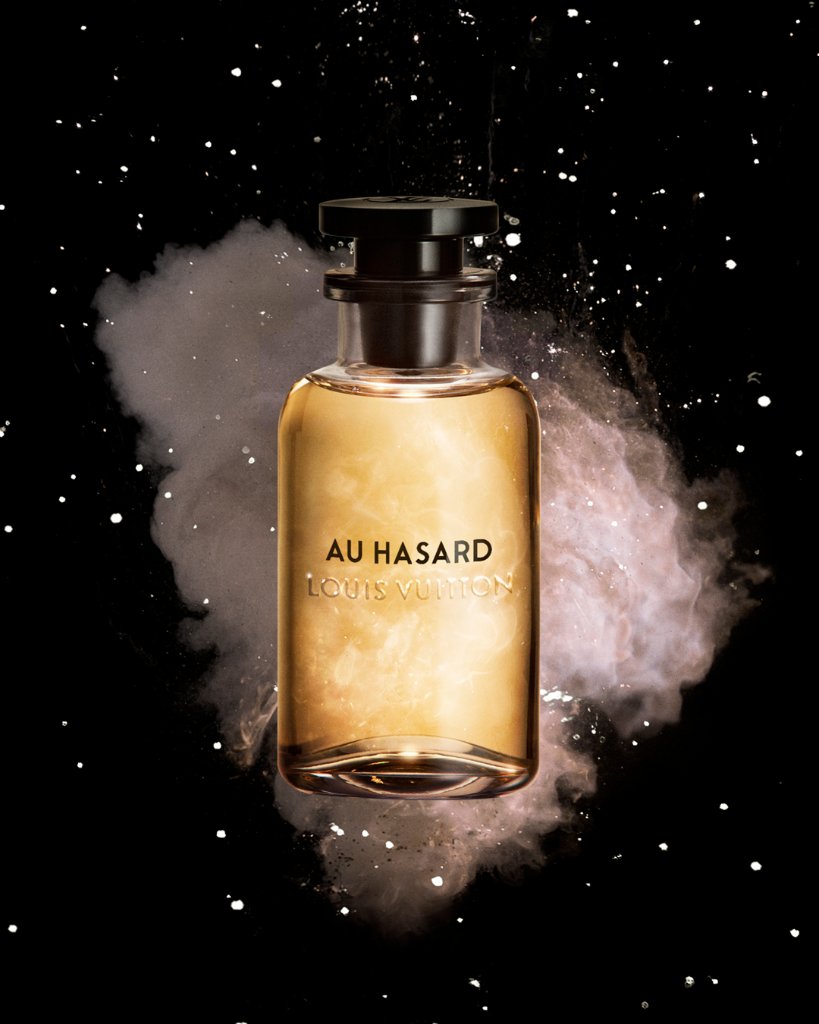
Louis Vuitton on X: #LVParfums for Men Chance encounters. Introducing Au Hasard by #LouisVuitton, a fragrance that embodies the thrill of the unexpected. Now available in stores and at /
Buy It Now 16d 6h
