Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
$ 83.00 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns
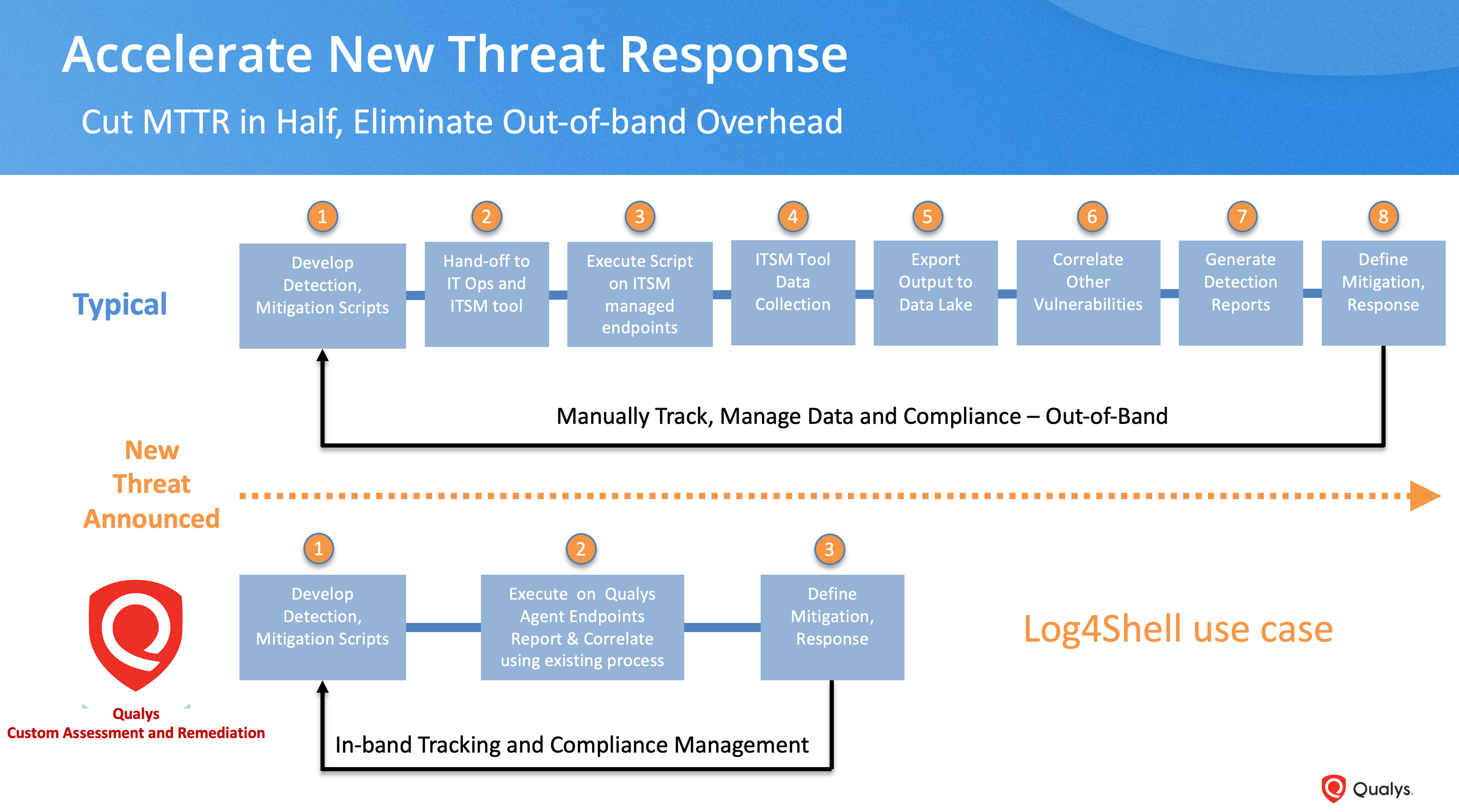
What's Next After Log4Shell? - vulnerability database
sample_code_2016/scrape_insert_wordpress
The role of endothelial MERTK during the inflam…
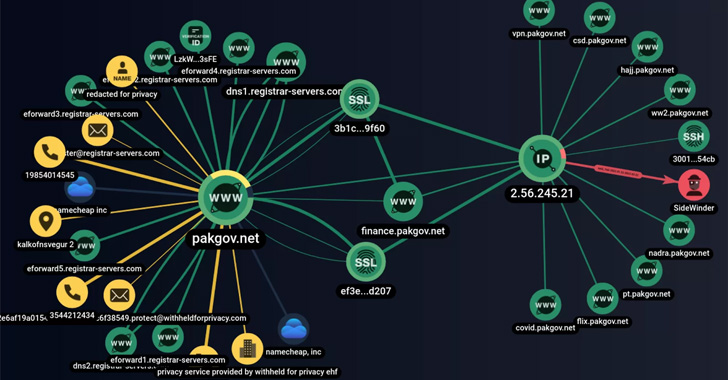
SideWinder Hackers Use Fake Android VPN Apps to Target Pakis
pydata2014-berlin/strata_abstracts.json at master · furukama
Microliths in the South Asian rainforest ~45-4 k…
The domesticated transposase ALP2 mediates form…
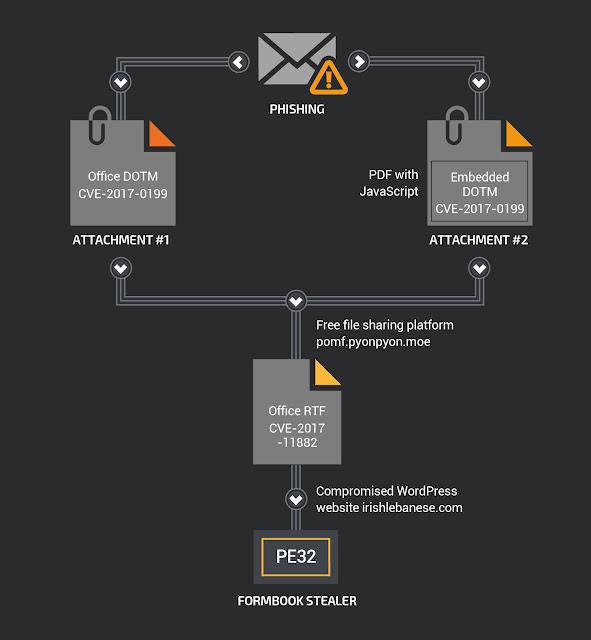
My Little FormBook - vulnerability database

C3-Fundamentals of Business MAths, PDF, Multiple Choice
VirtualAgent/data/GitHub_Jobs.json at master · Glavin001
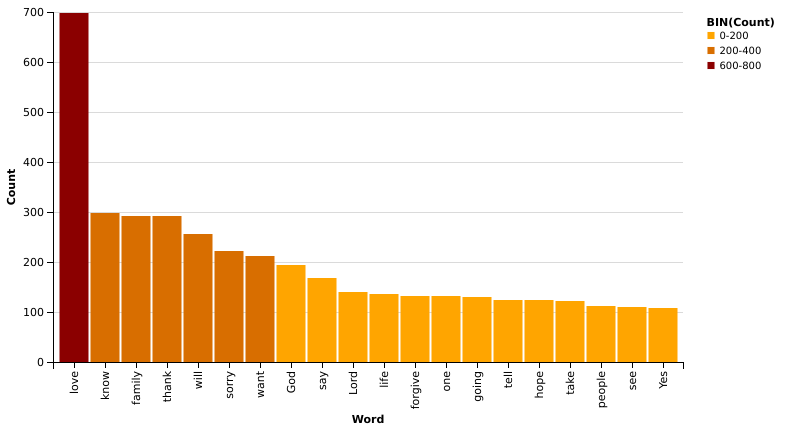
Exploration of Texas death row data
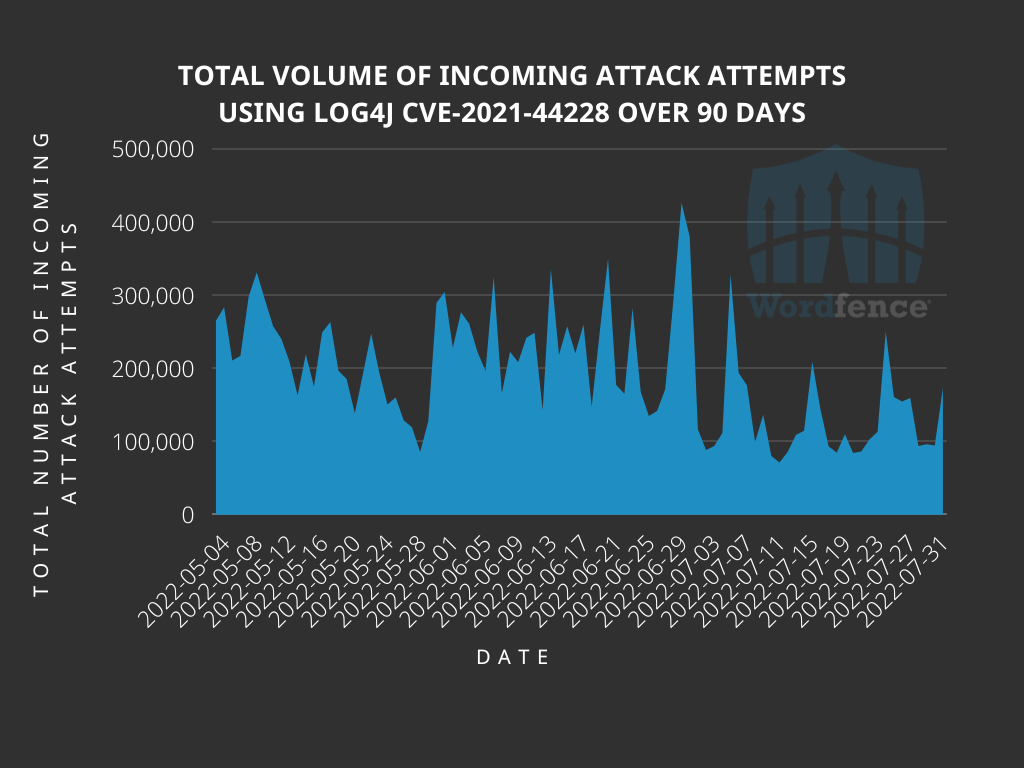
Analyzing Attack Data and Trends Targeting Log4J - vulnerability

R – James McCammon
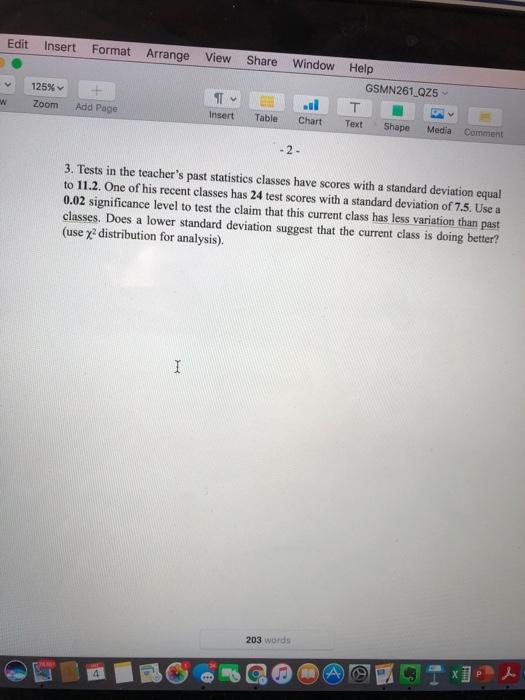
Solved Edit Insert Format Arrange View Share Window Help
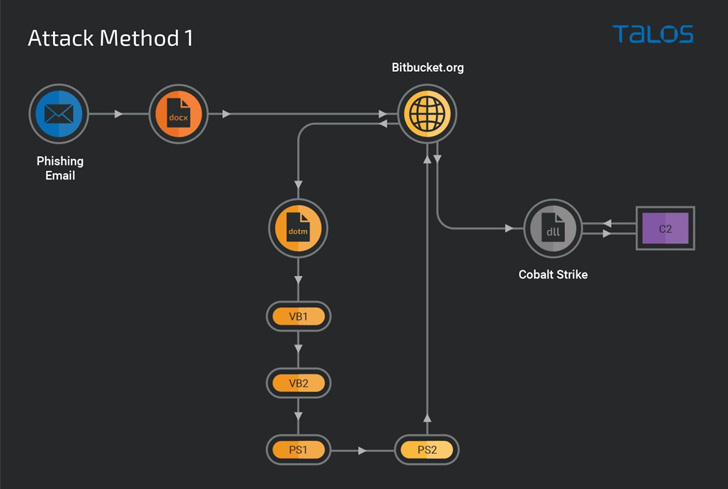
New Malware Campaign Targeting Job Seekers with Cobalt Strik
Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
- Best Price $ 83.00. Good quality and value when compared to palvarhaug.com similar items.
- Seller - 356+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Neverfull MM Damier Azur With Pouch for Sale in Long
Buy It Now 15d 18h -

New Retro Style Versatile Minimalist Design Coin And Card Holder Wallet For Students With Multiple Card Slots And Id Compartments. Fashionable Patchwork Clasp Closure Mini Leather Wallet
Buy It Now 9d 7h -

Louis Vuitton Men's Brown & Black LV Circle Belt Monogram Canvas M0017 – Luxuria & Co.
Buy It Now 14d 18h -

Women's Luxury Trainers
Buy It Now 13d 14h -

FWRD Renew Louis Vuitton Summer Stardust Monogram Nano Speedy Bag
Buy It Now 16d 18h -

Louis Vuitton Perfume AFTERNOON SWIM 200ml Empty Box, shopping bag and envelopes
Buy It Now 4d 17h -

Louis Vuitton Saint Cloud Mini
Buy It Now 22d 14h -

LOUIS VUITTON/RAINBOW MONOGRAM HANDBAG/Bag//WHT/Leather/Monogram – 2nd STREET USA
Buy It Now 7d 17h -

CANDYHONEY 2 Pcs Caramel Purse Organizer for LV NEONOE MM Bucket Bag Handbag Insert Soft Luxury Velvet Not Felt Organizer (Pink Neonoe MM) : : Clothing, Shoes & Accessories
Buy It Now 10d 23h -

Authentic LOUIS VUITTON Monogram Tambourine Shoulder Bag M51179 LV discontinued
Buy It Now 15d 23h -

Braided Updo The Teacher Diva: a Dallas Fashion Blog featuring
Buy It Now 17d 13h -

12 Best Hermes lindy 26 ideas hermes lindy, hermes lindy 26, hermes
Buy It Now 4d 12h -

How to tie a tie EASY WAY (Slowly & Mirrored) Windsor knot
Buy It Now 24d 22h -

Louis Vuitton Monogram Reverse Canvas Pochette Metis Bag - Yoogi's Closet
Buy It Now 24d 5h -
Ex-Manchester United star Memphis Depay shows off gruesome eye gash after fiery Lyon vs Marseille clash - Irish Mirror Online
Buy It Now 11d 19h -

Charles & Keith - Wikipedia
Buy It Now 4d 5h -
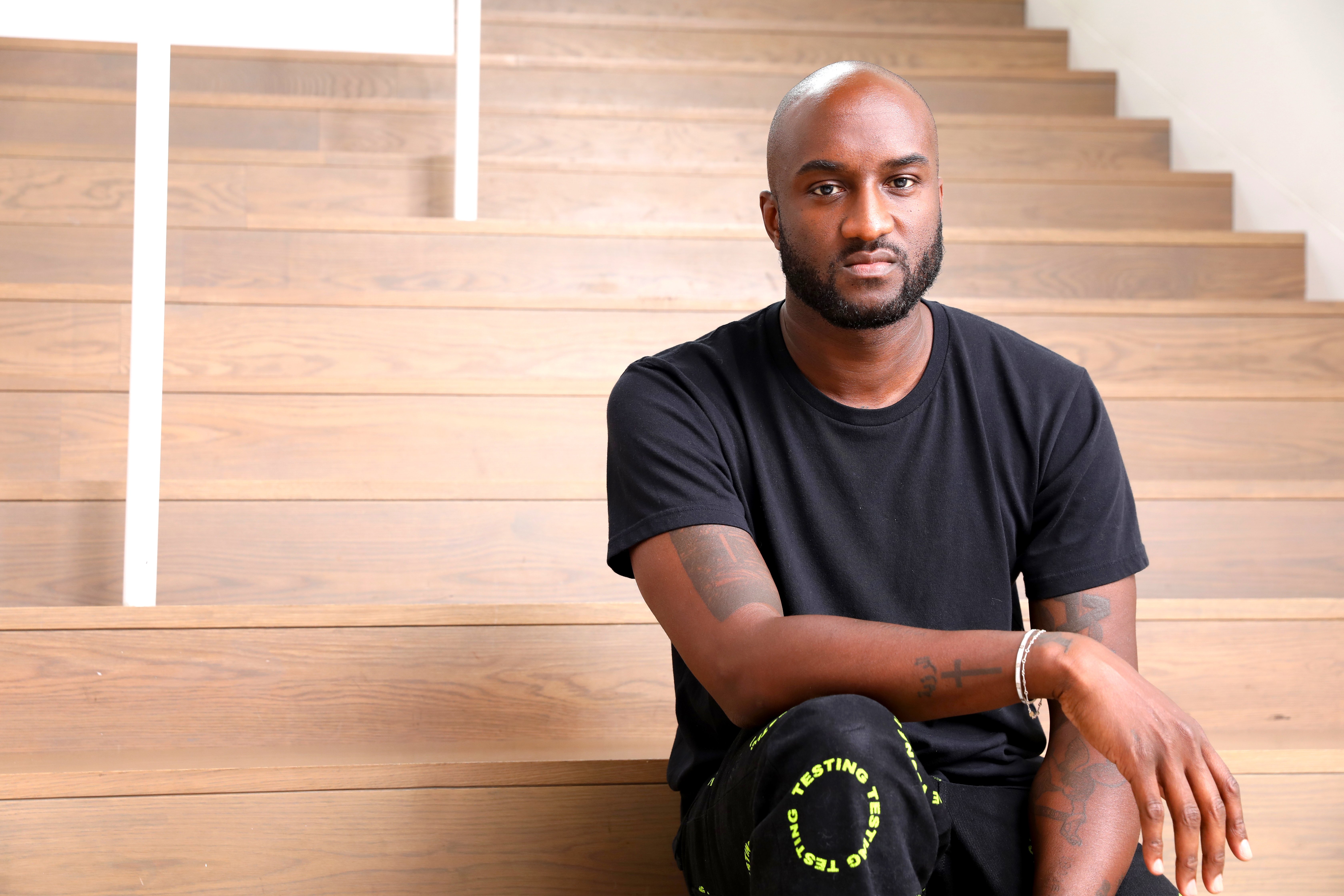
Virgil Abloh, Creative Genius Whose Vision for Fashion Transcended Boundaries and Crossed Into Art, Has Died at 41
Buy It Now 13d 9h -

Sunflower Decoration Rope Woven Tote Bag Rainbow-colored Rope Shoulder Bag Souvenir Crochet Bag
Buy It Now 16d 20h -

Are tucked-in football shirts coming back?
Buy It Now 28d 9h -

McLaren never expected F1 podium pace in Monaco
Buy It Now 28d 16h -

Breitling Top Time Deus Limited Edition A233101A1A1X1 One of 1500
Buy It Now 18d 20h -

Louis Vuitton Perfume Sample Men & Women Fragance 2ml BRAND NEW Authentic LV EDP
Buy It Now 9d 20h -

Nike Air Force 1 '07 LV8 - Nohble
Buy It Now 5d 18h -

3 Tips for Authenticating the Louis Vuitton Neonoe - Academy by FASHIONPHILE
Buy It Now 10d 22h
